Single sign-on authentication (or SSO authentication) has overthrown the traditional login process and completely changed the way people use the web.
Not sure what SSO authentication is? Not sure why should you care?
If you want users on your websites, interacting with your app, or signing up as customers, you can’t afford to stay in the dark any longer and jeopardize your potential success.
Running websites, developing apps, or creating an online business requires user authentication. Simply put, you have to know who’s using your site. Authentication is how you identify and track users, which is essential for both logistical and security reasons.
The only problem? Authenticating your site’s users means forcing them to log in with their email and a password which is one of the worst experiences known to man. Forcing users to remember a password is like a dentist’s visit, tax season, and a flat tire all rolled into one.
At Swoop, it’s no secret that we hate passwords with a passion as hot as the surface of the sun.
Ok, maybe we’re being a little dramatic, but we care a lot about this topic. We created an ultra-secure passwordless login tool because we believe the internet has outgrown them. Passwords slow us down, are much more vulnerable than most people think, and provide a terrible experience that users despise.
That’s also why we love SSO authentication. It reduces our reliance on passwords, makes the internet more secure, and simplifies an inconvenient, time-consuming process.
Maybe you’re a developer, online entrepreneur, or just curious about SSO authentication. You’ve probably got some questions, so let’s get to the answers. We’ll walk through these core topics:
Use the links above to jump ahead, or follow along from the top.
So what is SSO authentication?
SSO authentication allows users to log in once to access multiple applications, services, and accounts, even across different domains.
One example of SSO authentication that you probably use every day would be Google’s suite of online applications. Log into one and you’ve logged into all of them. Pretty easy right?
No need to re-enter your password every time you bounce between your Gmail inbox and Google Drive, for instance.
This offers major benefits for both users and website administrators. First of all, SSO eliminates the need to manually log into each separate application. This is a massive improvement to the user experience and encourages users to stay engaged with your website or apps.
In addition to reducing the need for multiple login steps, SSO authentication also means:
- Improved internal security for your site. With a centralized SSO system, it’s a lot easier to monitor user accounts across multiple applications. Plus, since new users only need to create one password, it reduces the number of passwords you’re responsible for protecting.
- Increased collaboration and efficiency. Large companies, universities, and government offices develop their own SSO solutions for this reason. For a more common example, think of how it easy it is to share Google Docs and spreadsheets with your Gmail contacts.
Say Goodbye to Passwords
and
Hello to Secure Logins.
Go passwordless and delight your users with secure and seamless one-click login.
How does SSO authentication work?
Here’s the SSO process boiled down to four steps:

- The user arrives on the website or app they want to use.
- The site sends the user to a central SSO login tool, and the user enters their credentials.
- The SSO domain authenticates the credentials, validates the user, and generates a token.
- The user is sent back to the original site, and the embedded token acts as proof that they’ve been authenticated. This grants them access to associated apps and sites that share the central SSO domain.
Here’s another, slightly more complex, way you might visualize this process:

I know this graphic looks a bit complicated but stay with me here! Each step in the process is represented by a numbered line above and corresponds to the step below.
- The user visits the target domain.
- They’re redirected to the SSO domain.
- The user signs in with their credentials and the SSO domain finds a match.
- The SSO tool requests an encrypted token from the authentication server.
- The user is redirected back to the target domain.
- The encrypted proves that they’ve been authenticated.
- The user can now freely access associated domains, too.
Token-based authentication is another important login concept (learn more here). SSO systems essentially rely on these tokens to “remember” that a user has already been allowed access to all of the apps associated with that central SSO hub.
Not too bad right? And with Swoop’s ground-breaking tech, it’s even easier than ever to get started with SSO authentication. Learn more about Swoop here.
Is SSO authentication secure?
The short answer is yes — SSO systems are very secure when implemented properly and used alongside other modern cybersecurity tools.
Here’s the longer answer. SSO authentication systems can boost the overall security of the internet for two main reasons:
- They reduce the number of weak passwords that people create and use all over the internet.
- They create more centralized systems that are easier for administrators to manage and protect.
However, there’s also some risk in centralizing multiple processes into a single system. If a hacker were to get into that central system or steal a user’s password, they’d have access to all of the apps and tools connected to that SSO system.
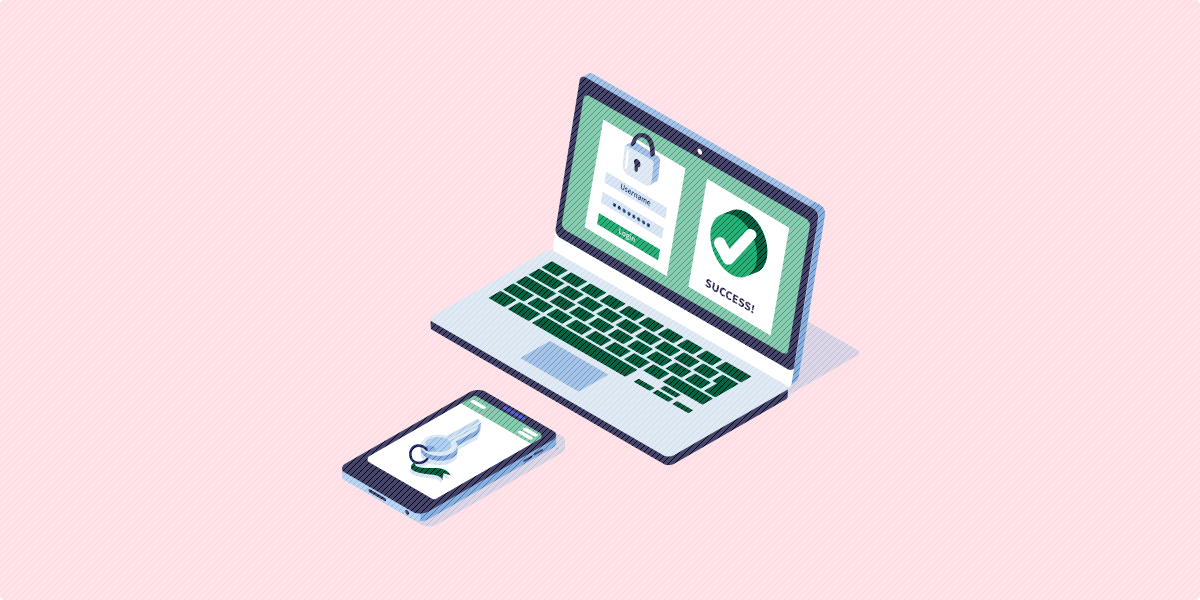
Thankfully, it’s easy to add extra security tools to an SSO login system. The best option? Two-factor login from Swoop. The main idea of two-factor login is to double-check your identity before granting access.
You might worry that adding a step will decrease the quality of the user experience, but remember that the SSO process is already extremely efficient for users.
The best part about implementing a two-factor login element to your SSO system, though, is that it doesn’t seriously affect the user’s experience. Two-factor login is quickly becoming the norm, and most users don’t mind completing a two-factor process once if it means they’ll stay safely logged in for an extended period.

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
What are the types of SSO authentication?
We’ve already covered the basic process of how SSO login works, but keep in mind that there are two different types of SSO systems.
We can generally divide them into internal and external single sign-on systems.
What’s internal SSO login?
Internal SSO systems are used by large companies, government offices, universities, and other large organizations. Here, they help users navigate easily between internal applications that the organization uses.
For instance, a university student might only need to log in once in order to access their class schedule, pay their tuition, and make an advising appointment — all through separate web apps.
Internal SSO systems typically need to be custom developed. This means they can be expensive and difficult to repair if broken, but they are very effective at streamlining internal tasks for users.
What’s external SSO login?
External SSO systems are user-facing and exist in free or paid web applications. The Google suite of web apps is the perfect example of external SSO. If you’re a developer or online small business owner who needs to manage users across multiple web apps or login portals, external SSO is the answer.
These login systems can be custom developed or implemented using additional authentication tools, like Swoop two-factor.
For your users, the benefits will be immediate. Streamlining login provides a huge improvement to user experience more generally. On your side, centralizing your whole login system will seriously reduce the burden on your servers.
There you have it — the basics of single sign-on authentication. You now have the power in your hands. You can drastically improve your website’s user experience, starting today.
What are you waiting for? Start with implementing SSO authentication by giving Swoop a try. Your users will thank you.
For more useful articles on website authentication and password security, check out these additional resources:
- 7 Ways to Create a Modern Password and Username Login Process: Looking for more ways you can improve your users’ experience? Get our 7 tips to make the login process quick, simple, and—most importantly—secure.
- What Is OAuth? | Learning the Basics of Open Authorization: Organizations that are interested in collaborating with third-party services, like social media sites, this article is for you! Learn everything you need to know about offering SSO authentication on sites your organization doesn’t own, otherwise known open authentication.
- Password Alternatives for Nonprofits and Businesses: If you want additional ways you can remove passwords from the login process, check out our list of password alternatives. Combine them to create a complete solution.