With online security becoming a popular topic, the importance of implementing secure authentication methods on websites is more crucial than ever. By ensuring that your users’ information stays safely behind your website barriers is about more than just maintaining your users’ trust. Without the right security measures in place, your users’ accounts could be easily compromised.
As a result, sensitive information on users’ credit cards, contact information, and so much more could be in the hands of cybercriminals.
While many organizations aren’t quite comfortable with the idea of removing passwords entirely, there are additional measures they can use to ensure that cybercriminals can’t access users’ private information.
One solution? Two-factor authentication.
You’ve probably heard this term mentioned when the question of password security is brought up, but what is two-factor authentication and how can it make your users’ accounts more secure?
You’re in luck! We’ll cover these questions and more in this in-depth look at two-factor authentication.
Feel free to read our entire guide, or jump down to the following questions you need answered:
- What is two-factor authentication?
- How does two-factor authentication work?
- Why should websites use two-factor authentication?
- What types of two-factor authentication can websites implement?
- How can organizations find a two-factor authentication vendor?
Before you get started, brush up on how website authentication normally works with our complete guide!
Keep reading to learn the ins and outs of two-factor authentication.
1. What is two-factor authentication?
Simply put, two-factor authentication, otherwise known as two-factor verification or 2FA, is an additional step in the login process that requires users to present a piece of information that only the user should have.
This “piece of information” can be anything from a one-time passcode to a physical token (for more types, jump to section four) that acts as a second confirmation to verify users are who they say they are.
Essentially, a true form of two-factor authentication requires the user to have:
- A password and username (what they know)
- A passcode that was sent to their mobile phone, email, or authenticator app (what they have)
In the standard login process, a user can access their account by entering a username and password—no additional steps required. However, in two-factor authentication, the user has to complete the second confirmation step.
Two-factor authentication has been around for some time, and you’ve probably used a version of this authentication method to log into an email or bank account or make a credit card purchase.
Two-factor verification vs. security questions
While two-factor authentication does require two steps, it shouldn’t be mistaken for security questions or other prompts (like completing a math problem).
Security questions have a similar purpose, but are, ultimately, less secure than two-factor authentication because they’re “what you know” factors. By doing a little online digging, a hacker can easily guess the correct answer to your security question, whereas obtaining your phone would be much more difficult.
Additionally, the other prompts that users are asked to complete are usually there to ensure that the login request was made by a human.
To sum it up: Two-factor authentication is an additional step users must take after entering in their credentials. To be considered a true form of two-factor verification, the second step must require the user to have something like a passcode retrieved from their mobile device or email account.
Say Goodbye to Passwords
and
Hello to Secure Logins.
Go passwordless and delight your users with secure and seamless one-click login.
2. How does two-factor authentication work?
Depending on your website’s specific needs, you may decide that you want to implement two-factor authentication as a required step for every login attempt or just for attempts that have been flagged by your system. For instance, many bank accounts only require users to complete a two-factor step if they’re logging on from an unrecognized device.
Keep in mind: while two-factor authentication does offer an additional layer of security, in most cases, it also requires the user to complete another step, which can make the login process more time-consuming.
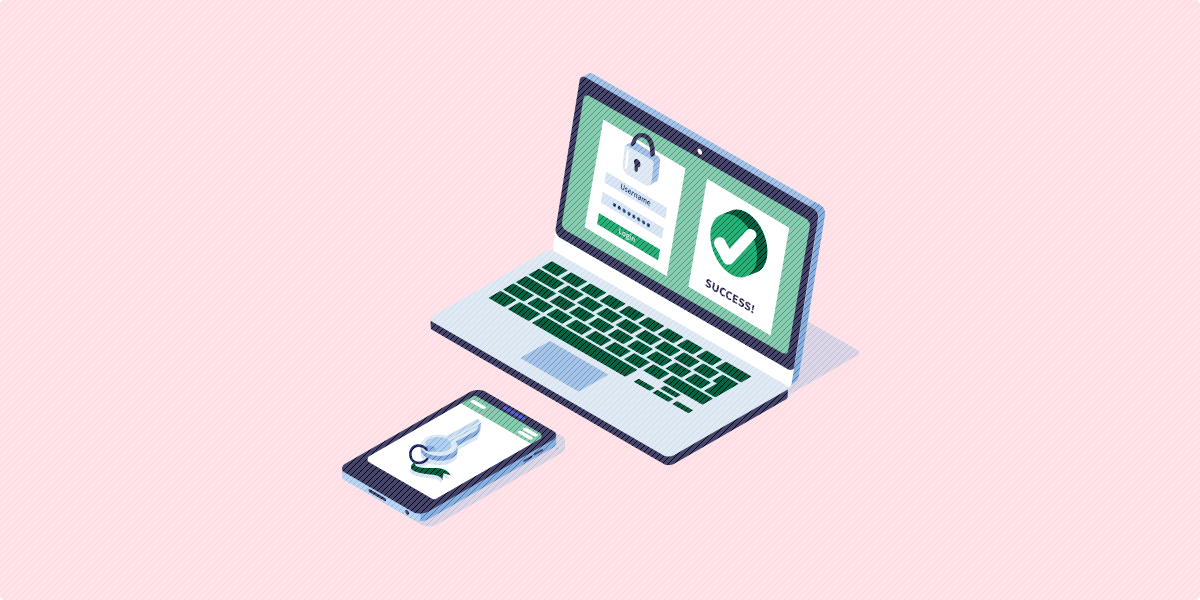
Once you’ve implemented two-factor authentication, here’s how the process would look using your cell phone:
- You land on the website’s login screen and enter your username and password to request access to your account.
- If you’ve only enabled two-factor authentication to activate if the request has been flagged, the system will determine if you need to complete the additional verification step to ensure you’re not a hacker.
- A code will be sent via text message to the phone number you provided when you created the account. During this time, you’ll be directed to a second login screen prompting you to enter the code.
- Once you’ve entered your passcode, the system will verify that the code you enter is the same as the one that was sent to you.
- If there’s a match, you’ll be able to access your account.

Another key factor to note: websites can’t just set up two-factor authentication without some participation from the user. Let’s go back to the phone example. If the user hadn’t included a phone number when he or she signed up the account, the process wouldn’t work.
To sum it up: Two-factor authentication is something that must be authorized by users before it can be implemented and requires two credentials to access their accounts.
3. Why should websites use two-factor authentication?
Adds another layer of security to insecure passwords
It seems we can’t go a day without news of a new password breach, and with more and more accounts becoming compromised, it goes without saying that passwords aren’t secure.
Even if every person used strong passwords, our accounts could still be easily cracked using brute-force attacks and cracking technology.
Whats more? Most users don’t create strong passwords. In fact, nearly every account created can be accessed using a password from a list of 10,000 most commonly used credentials.
Despite their vulnerability, passwords are used on countless websites to authenticate users. As a result, two-factor authentication is a way to add an additional security measure.
Even if an authorized user obtains your account credentials, you’re protected because the hacker will need access to the second verification step to enter your account.
Think about it this way: even if your website falls victim to a password breach, the accounts using two-factor authentication will still remain protected. It’s still recommended that donors change their passwords after a breach, though.
Strengthens your organization’s internal accounts
We’ve been talking a lot about your users’ experience, but two-factor authentication can also be implemented internally. Every time an employee logs into their email or project management account, they can be asked to complete an additional verification step.
The truth is that all the concerns of password security easily affect your employees as well. Not to mention, they have multiple accounts to manage and it can be difficult creating secure passwords that are easy to remember.
Still not convinced that password security could affect your organization? Check out this article to see all the ways your employees’ passwords could be compromised.
Even if your organization trains staff on how to create and manage secure passwords, there is no way to guarantee that all your employees will follow the rules. Two-factor authentication can act as a failsafe when things slip through the cracks or when a cybercriminal hacks an employee’s account despite the strong password.
Additionally, two-factor authentication can make your employees’ jobs more convenient. Let’s say that users are only able to access their accounts on an office computer for security reasons. As a result, your staff is limited on where they can work and how they can access information. With mobile two-factor authentication enabled, there’s less of a security risk for employees to access data outside of their office computer, allowing them access to important information on the go.
To sum it up: Implementing two-factor authentication as both an internal and external security measure can further protect your users’ and employees’ accounts.
Bonus! For more information about securing your organization’s website, keep reading Swoop’s best practices for username and password logins.
4. What types of two-factor authentication can websites implement?
Organizations have several two-factor authentication options to choose from. Ultimately, deciding on the best fit will depend on your organization’s needs.
Let’s dive deeper into three different types of two-factor verification:
Completing a two-factor authentication via an email account may be the most universal method because most people access their email on a daily basis.
The idea is fairly simple:
- After users enter their usernames and passwords, they’ll be sent an email.
- Generally, the email will include a code that the user must enter or a link that allows the user to access their account.
With a provider like Swoop, however, the process works differently. We built our system to work like two-factor authentication, but without the added step of accessing your email’s inbox and entering a passcode into the login screen.
When users want to donate to an organization via text-to-give, for example, here’s how the process will work:
- The user will text the donation amount they want to give as the first form of authentication.
- Swoop’s system sends the user a link that directs users to a pre-written email with the details of the donation.
- All the user has to do is hit “send” and the donation is verified and confirmed.

Our technology uses three levels of security to verify that the request (in this case a donation) was authorized by the user. And if there is ever any uncertainty, Swoop will send users a text message asking them to confirm or decline the request.
Best of all? Donations aren’t the only requests our email authentication system can handle. Everything from traditional accounts to e-commerce sites can use Swoop’s services.

SMS
We’ve talked a lot about the SMS two-factor authentication process because it’s one of the most widely used types. Sending a code via text message is a great way to ensure that the person requesting access to the account is an authorized user since it would be difficult for a hacker to obtain your phone.
However, SMS two-factor authentication doesn’t rank as well in terms of user experience. First, it requires the user to always have their phones with them (which isn’t an unreasonable request). The user’s phone also needs to be able to accept text donations (some plans still charge a fee for every text message sent) and have cell service to receive the text. Depending on the situation, this might not always be possible.
Second, it creates an additional step in the process. When compared to Swoop’s process that can be completed in two steps, having to wait for the code to be sent to your phone and entering the code on the login screen can be a time-consuming process.

Authenticator App
Authenticator apps work in a similar way to SMS two-factor authentication. Instead, of having the passcode sent to your cell phone via text message, the code is generated locally on your smartphone.
Password authentication apps use a cryptographic algorithm to produce a one-time passcode.
How does the app connect to your account?
When you create your account, a secret key (also known as a seed) is generated and stored on the server. The key is sent to your phone usually in the form of a QR code and imported to your authenticator app.
When you sign into your account, the authenticator app will scramble the seed together with the time and date of when you attempted to log in.
The benefit of using an authenticator app versus SMS is that you don’t need cell service for it to work.
However, like SMS two-factor verification, the process requires more time and effort on the user’s part.

To sum it up: There are three main types of two-factor authentication, and each option comes with its own set of pros and cons. It’s up to your organization to determine which type of authentication method will work best for your organization.

1-Click Login is a simple & secure password-free authentication service.
With our patented technology, your website can improve security & increase customer conversion by removing passwords.
5. How do organizations find a two-factor authentication vendor?
Implementing two-factor authentication into your website’s authentication system can be a huge ordeal if you decide to do it on your own.
That’s why many organizations choose to work with two-factor authentication vendors.
When you hire a vendor, their team of experts will:
- Assess your website’s infrastructure to determine what capabilities your website can support.
- Implement their two-factor technology into your organization’s website.
Two-factor authentication vendors not only have the expertise to implement this new security protocol into your website, but they also have a strong foundation to work from.
For instance, Swoop’s services provide organizations with access to our secure API, which we’ve developed and modified to provide the best functionality possible.
You’ll need to determine which type of two-factor authentication you want to implement. While some vendors may offer variations of each type, may vendors specifically focus on one type of method.
Without a clear understanding of what you want, the process of implementing an authentication method could take much longer than you planned.
To sum it up: When it comes to implementing two-factor authentication, we recommend that you hire a vendor to ensure that your system works seamlessly.
Now that we’ve covered everything from the basics of two-factor authentication to shopping for a vendor, you can boost your website’s security. A secure infrastructure can help your organization establish your users’ trust and protect against data breaches. Good luck securing your site!
For more information on password security, check out these additional resources:
- How Strong Is My Password? | “Not Very,” Security Experts Say. If you’re interested in learning more about why passwords aren’t secure, this is the article for you! Top security experts explain why passwords are obsolete and provide new login solutions.
- How Does Single-Sign-On (SSO) Authentication Work? Two-factor authentication isn’t the only type of authentication method that websites can use to improve their security. Check out how single-sign-on authentication can consolidate the number of passwords a user has to manage.
- Email Password Breach: 8 Ways Websites & Users Can Stop It. No one wants to have their email accounts compromised. This article walks through several ways websites and users can protect their email accounts.